Episode Transcript
Transcripts are displayed as originally observed. Some content, including advertisements may have changed.
Use Ctrl + F to search
0:01
I don't want my medical device to kill
0:03
me because somebody hacked it. They can send
0:06
wireless alerts. So if they detect
0:08
a problem, they can send it.
0:12
Hello
0:12
and welcome to Insight Story,
0:14
tech trends unpacked for business leaders. The
0:17
podcast that gives you the insight you need
0:19
to make the right strategic decisions about
0:21
how to use the right tech for your organization.
0:24
Brought to you by Kaspersky,
0:25
the cybersecurity specialists. This
0:27
time we're asking
0:29
how can you safely get the benefits
0:31
of the industrial Internet of Things?
0:38
Now, the industrial Internet of Things, or IOT,
0:40
is the place where the Internet meets industry.
0:43
Smart devices sharing data to help companies
0:45
make better decisions. But what
0:47
about keeping those systems secure? In a bit,
0:50
I'll be talking to two people about exactly
0:52
that. Chris Kubeska from HyperSec,
0:55
whose interest in digital security started
0:57
when she hacked into the US Department of Justice
0:59
when she was 10. God, I was playing the
1:01
recorder at that age. And Alison
1:04
Peace from Medtronic, who is responsible
1:06
for helping thousands of hearts to
1:07
keep on beating. But first, to make
1:10
sure we understand what we mean when we say I-I-O-T,
1:13
we have our own smart device.
1:16
I am Dolly, your insight assistant.
1:19
Hello Dolly. Thank you for coming by. Hello
1:21
Susie. Now this time, I need to know
1:24
more about the industrial Internet of Things,
1:26
the I-I-O-T. I-I-O-T
1:28
refers to any network of Internet connected
1:30
machines that share information.
1:33
Sensors and devices collect real-time
1:35
data from Internet connected physical
1:38
assets. Data is uploaded
1:40
and analysed. This tech is
1:42
used in sectors like farming, manufacturing,
1:46
healthcare and transport. So
1:48
this is a lot more than your smart fridge being
1:50
able to tell you that you're out of milk.
1:53
The principle is the same, but I-I-O-T
1:56
is at a bigger scale. Devices
1:58
can share data in real time. This
2:01
can all happen
2:03
without a human. So
2:12
it's about efficient use of resources? Yes,
2:15
and also safety. IIOT
2:18
can check if a machine gets too hot
2:20
or if there's a gas leak in a factory.
2:23
It helps prevent accidents. So
2:25
talking of safety, what happens if someone
2:27
hacks into one of these systems? IIOT
2:30
systems must be extremely secure.
2:33
Use in question to protect data
2:35
and have security teachers work strong
2:38
passwords, legal and acting, and
2:40
follow-up to keep hackers out. Alright,
2:44
have you ever been hacked? Thank you
2:46
for your concern, but I have extensive
2:48
safety mechanisms in place. I
2:50
am very secure by design. I'm
2:54
very glad to hear it. Thank you for your help. Goodbye. So
2:59
here to talk more about getting the most out of
3:01
the IOT and doing it as securely
3:03
as possible, we have Kris Kubezka.
3:06
She's a computer security researcher and cyber
3:09
warfare specialist who no longer
3:11
hacks into those government departments unless
3:13
they ask her to. She has provided
3:16
essential support to many companies and countries,
3:18
including getting the Saudi company Aramco's
3:21
network back up and running after it was
3:23
hit by one of the world's most devastating Shamoon
3:25
attacks. That's an aggressive malware
3:28
virus. She's now based in the Netherlands
3:30
and is CEO of HyperSec, a
3:32
security firm she founded in 2015,
3:35
and the author of Hack the World with OSINT,
3:38
designed to help companies protect their systems.
3:41
Hello, Kris. Hello, everyone, and thank you
3:43
so much. This is wonderful. And
3:45
Alison Peace, who is patient management
3:47
operations manager for UK and Ireland
3:49
at Medtronic. They're a global developer
3:52
and producer of medical devices and therapies
3:54
such as insulin pumps, pacemakers
3:56
and implantable defibrillators. Their
3:59
equipment is already. making full use of this
4:01
kind of connectivity. Hello, Alison.
4:03
Hi, thanks for having me. Happy to be
4:05
here today. So starting with you, Chris, your
4:08
focus is on the safety and security of networks.
4:10
But before we talk more about that, what kinds
4:12
of industries are really making the most use of this technology?
4:15
One of the industries that is doing this is,
4:18
for example, the maritime industry. So
4:20
if you want to know, should
4:23
that ship go through that storm to save
4:25
fuel, or where the whole crack up,
4:27
they now have IIOT sensors
4:29
that are placed on the hull to report
4:32
back. Also space, big
4:34
into space, and space is actually propelling
4:36
us towards the normalization of
4:39
usage of things like 6G and 7G.
4:41
And 6G has direct
4:43
application to in-body
4:46
internet of things, medical devices, from
4:49
nuclear power plants, water, agriculture,
4:52
as you had mentioned. And these types
4:54
of things can unfortunately be manipulated
4:56
for nefarious purposes,
4:59
because I have to put my evil devil horns
5:01
on for the cyber warfare part. It's a very
5:03
interesting space. Pretty widely varied
5:06
uses of industrial IOT. And you were
5:08
talking about medicals. So turning to you, Alison,
5:10
tell us a bit more about Medtronic and the devices
5:12
you make and the kind of data that you're providing.
5:15
The part of Medtronic that I work is cardiac rhythm
5:17
management. So these cardiac devices help
5:20
people with slow hearts, with fast hearts,
5:22
with hearts that may
5:24
stop abruptly, you know, like a cardiac
5:26
arrest. In the UK alone, there's
5:29
probably more than 100,000 patients
5:32
in a year receiving some sort
5:34
of implanted cardiac device. These
5:36
patients have then a lifetime
5:38
of constant hospital checks. So
5:40
you can sort of start to sense the burden that
5:42
that places on the healthcare services. So
5:45
remote
5:45
monitoring for cardiac devices came
5:47
about almost 20 years
5:50
ago, but in a very basic form. The
5:52
devices are now more efficient, they can send
5:55
wireless alerts. So if they detect
5:57
a problem, they can send it, the patients
5:59
are better.
5:59
look tester, the outcomes are better, you
6:02
know, they use healthcare less because
6:04
they don't need to go into hospital. But what's
6:06
also essential is, as Chris alluded to,
6:08
that these things are safe. You
6:10
know, you're no longer keeping the patient data
6:13
within the
6:13
four walls of the hospital. So, Metronica
6:16
really giving us at the forefront of the
6:18
telemedicine revolution. But that security
6:20
is quite important. So, turning to you, Chris,
6:22
let's talk about some of the security measures
6:25
that smart system because it's involving people,
6:27
access control, encryption, obviously very
6:30
important with those devices. What
6:32
do you think of the focus areas for anyone setting
6:34
up this kind of system to be aware of from the
6:36
security side? Well, understand
6:39
that your procurement department is going to be
6:41
looking for the best deal, which is going to be the least
6:43
expensive deal. Your attorneys,
6:46
both in-house and externally, may
6:48
not have enough experience specifically
6:51
with cyber or privacy. And that's quite important
6:53
with medical. The best deal might
6:56
mean that someone didn't look at the
6:58
fact that you didn't require an annual
7:01
report done by an external, say,
7:03
penetration company or, you know, risk company,
7:06
whatever might apply into
7:08
that so that you know what you're getting from your supplier.
7:11
A lot of the IoT and industrial
7:13
IoT systems, they will come
7:15
with an older version of, say, Linux
7:17
kernel. And what this means is you're
7:19
getting an older operating system that
7:22
doesn't have all of the various security
7:24
settings you would want out of the box. And
7:26
if you don't know how to apply those things, or
7:28
if the company that you bought it from doesn't have
7:31
a secure way to update
7:33
the software because, you know, things change, things
7:36
get tweaked. Well, same thing you have to do with your
7:38
security settings and also your privacy
7:40
settings because the laws are changing.
7:43
These are some of the risks. Know what you're buying
7:45
so that you can actually plan ahead
7:48
and mitigate and minimize for those risks. Some
7:51
of these technologies we're talking about, both
7:53
medical and other industries, they've never
7:55
been placed on the internet, have they? They haven't even
7:57
been designed for the internet world. particular
8:00
risk for those types of companies, they need to
8:02
invest more. The internet in and
8:04
of itself was not meant for the internet in and
8:06
of itself, how it is right now. This
8:09
is a good question for Alison. What
8:12
are these additional things that you have to put
8:14
in place for devices that
8:17
are now fitting in and trying
8:19
to innovate and help human beings but
8:21
weren't meant in particular for these types
8:23
of systems to connect to?
8:25
The devices themselves, they're completely
8:27
different now to those devices that I talked about 20
8:30
years ago. It's been important to incorporate
8:32
an
8:32
encryption module into
8:35
those devices to make
8:36
sure that actually there's no readable data
8:38
from the devices. The devices themselves aren't connecting
8:40
to the internet. They're using a pass-through,
8:43
a monitor or an app. The data
8:45
that's in the device
8:46
is encrypted and the data
8:48
that goes through the best-side
8:50
monitor or the app is
8:52
pass-through. Someone was using a patient app
8:55
and they lost their
8:55
mobile phone. They're not going to find anything
8:57
on that phone. The clinician accesses
9:00
the data through a secure website, password
9:02
protected and also in
9:04
all those different steps, whether it be in the
9:06
device, whether it be in the patient app and
9:09
then at the secure server where the clinician
9:11
is accessing the data, it needs to be
9:13
as secure as it can be. I know, Chris, there's
9:15
people like you that you hope
9:18
to not be able to hack into the systems and
9:20
companies like Natronic obviously
9:22
have similar experts
9:25
that are always trying to challenge the
9:27
things that are produced. And how do you help the
9:29
customer, the end customer, the patient have
9:32
that trust that what they're putting into their body,
9:34
sometimes physical devices, is
9:36
trustworthy? How do you communicate
9:38
that back to them? I think just reminding
9:40
them, you know, we are not in charge of
9:43
what the hospitals do. We supply these services,
9:46
but what's really important to mention
9:48
and the same, I'm sure, is true of many countries
9:50
that can only speak for the UK and Ireland here where
9:52
we have national health services
9:55
with really strict controls on what
9:58
third parties they'll engage with, what systems they can use. and they
10:00
use, there's all these rules and regulations and
10:02
things that you have to have in place in order to
10:05
partner with hospitals. And if you
10:07
don't have it, you're told to go away
10:10
and come back when you've got it. Sure. And as Alison says,
10:12
Chris, these standards are very important.
10:14
So what can companies do regarding testing
10:17
and standards that they should be expecting from third parties
10:20
to make the devices more secure? Some
10:23
of the things that Advise Incorporated
10:25
is looking at the contract.
10:28
It should fit a minimal amount
10:31
of encryption as per the date
10:33
of this contract. So you're not specifying
10:36
it's got to be this number, that number,
10:38
something technical, but
10:41
what the requirements
10:43
and what the standards are at that time. So that
10:45
when you renew, the expectation
10:47
is to still keep those standards.
10:49
Little things like that. Obviously,
10:52
ensuring your suppliers are also
10:55
practicing good data security and
10:57
data privacy because you don't want your intellectual
11:00
property somehow being waylaid
11:02
between the factory floor and
11:04
someone else getting a chip set. Even in the space
11:07
industry and the aviation industry,
11:09
they have found fake parts and it's
11:12
a big problem. So these are some of the other
11:14
things that a board might not think
11:16
about, which would be
11:17
quite damaging to the reputation. Definitely
11:20
engage with people like
11:22
me. There's other groups like the
11:24
biohacking group, which
11:26
goes
11:26
around to various different conferences.
11:28
So those are some of the
11:30
things as well as ensure
11:33
that you have enough
11:35
of a relationship with the supplier that if something
11:38
comes out, if someone contacts
11:40
you and says, hey, we can do this, that and
11:42
the other and you're like, uh-oh, be prepared,
11:46
have a sufficient responsible
11:48
disclosure policy. For example, in the Netherlands,
11:50
it's a requirement for most companies to
11:52
have that. That's not international,
11:55
but have that preparation and know that you can
11:57
contact your supplier. You,
12:00
Alison, there's many stats out
12:02
there about the huge volume
12:04
of IoT devices out there in the world. 50 billion
12:08
is one stat and many terabytes
12:10
of data being processed all the time. In
12:13
the case of Medtronic, where does that data
12:15
actually go and how are you protecting it?
12:17
Obviously, Medtronic is a US company.
12:20
I mean, it's
12:20
a global company, but its home is in the US.
12:22
And what was really important when we started
12:25
using remote monitoring,
12:26
because the server at the time
12:28
was in the US. And as we've talked about,
12:30
there's different data,
12:31
privacy and security laws, you know,
12:33
when you travel globally, there's different
12:35
sort of rules and regulations. And what
12:38
wouldn't have flown at all is
12:40
coming to Europe with, we're going to send
12:42
all this data to the US and it's going to sit there.
12:45
So there was a lot of investment in having
12:47
a European housing of that data.
12:50
And Chris, turning to you, you've talked about some of
12:52
the big challenges that are out there with the
12:54
industrial IoT systems. But what's the best
12:56
way for companies to actually address these
12:58
challenges? And where could they get some
13:01
advice
13:01
from trusted
13:02
parties? There are a few different
13:05
trusted parties that you can try to
13:07
look at. Try to set up a relationship
13:10
with the country that
13:12
your main operations are with. And what I
13:14
mean by that is in case there is some sort
13:16
of cyber issue, you
13:18
can contact what's called a Computer
13:20
Emergency Response team in the
13:23
United Kingdom. They can actually
13:25
put you in touch if you don't already have
13:27
that relationship
13:28
with some of the providers
13:30
of various trusted services when
13:33
these types of cybersecurity incidents occur.
13:36
It's good to go,
13:37
hi, I'm company Zed
13:40
or Z for the American listeners. And
13:42
this is our type of operation. Could we
13:45
set up a meeting to know what websites
13:47
we'd be looking at for alerts? What should
13:50
we do if something happens, etc,
13:52
etc. That is one of the biggest things
13:54
because that can open doors if you don't
13:57
really know where to look. But try to
13:59
do this ahead of time. Also, your lawyer
14:02
will suddenly become your best friend. I
14:04
know that's not a common saying, but
14:06
your lawyer, even though they may not have
14:09
experience with cyber, they will have colleagues
14:11
that they can put the word out to in a private
14:13
way.
14:14
You talked about a lot of different industries that you've
14:17
worked in using IoT. Do
14:19
you think the technology is actually moving faster than
14:21
the law in this case, or are we keeping
14:23
a good pace? Oh, yeah, definitely
14:25
moving faster than the law. But that's what
14:27
you get from technological innovation.
14:30
Although it is moving at a fast pace, there
14:33
are some guidelines, frameworks,
14:36
and more and more governments and industry
14:38
are aware of these potential risks. So
14:41
the likelihood of something terrible,
14:44
terrible happening, lessons and lessons and
14:46
lessons, we're actually tackling
14:48
this problem. And so, Alison, Medtronic's a
14:50
global company, and that means you're dealing with
14:52
a lot of different rules and regulations
14:55
when it comes to your suppliers and the data.
14:57
So standardization plays a role, but also
15:00
what in the security industry, of course, secure by design.
15:02
So building that into the
15:05
start of the project. Of course, you
15:07
know, we can come out with national
15:10
legislation that says, I want
15:12
the data to come from your device in this
15:14
format.
15:15
And actually, our devices are designed to send
15:17
it in this format. It even is beyond
15:20
even the security of the data. It's
15:22
often the format of it. At the start,
15:24
those first wireless devices that we
15:27
launched almost 20 years
15:29
ago now are
15:30
not the wireless devices that we sell
15:32
now. You
15:32
know, everything's changed about them, even
15:34
the method of communication, and not
15:36
just the data security,
15:38
but also efficiency on that device.
15:40
So Chris, what are your thoughts on what those selling
15:43
industrial reality devices, what should they
15:45
be doing as part of their best practice? I
15:48
think they should start applying
15:50
what I would call easy standards. We had
15:53
a workshop at the United Nations
15:55
Internet Governance Forum about this with
15:57
Internet of Things and industrial Internet of Things.
15:59
It's hard for both consumers and companies
16:02
to know, does it meet a minimum
16:04
level of standards for security?
16:06
Can it be updated, for example, all
16:09
the way up to, say, something you would use for
16:11
medical stuff? This would be the highest standard.
16:14
I don't want my medical device to kill me because
16:16
somebody hacked it. And we had proposed
16:19
something as easy as, say, a traffic light system
16:21
or something like that so that
16:23
you know, all right, it meets at
16:25
least this minimum standard. It
16:27
might cost 10 euro more, but you
16:30
know that the risk is
16:32
probably more
16:32
minimized. So I would love to
16:35
see as an industry group for
16:37
some of those things
16:38
to start occurring.
16:39
So, Alison, just turning to you finally,
16:42
you talked about some very exciting stuff that's happening
16:44
right now at Medtronic, but what are your plans for
16:47
the near future? I mentioned a patient
16:49
app.
16:50
This is new to us, you know, and at the moment
16:52
is with Apple and Samsung. And also
16:55
the population will see growth. I
16:57
think 10 years ago, maybe 3% of
17:00
people over 65 had a smartphone, whereas
17:02
then 10 years on, they're the people who were 55 before,
17:04
you know, and now it's more sort of 80, 90%. It's
17:08
the healthcare outcomes of patients that are more
17:10
engaged in their healthcare
17:12
with always awareness
17:15
of how secure we need to be, obviously.
17:17
Great. So we've had a great conversation today. Thank you for
17:19
joining me. We always like to give an insight story,
17:22
a final thought, that golden nugget
17:24
of insight. So if you were going to give
17:26
a piece of advice to perhaps a CEO
17:29
of a company who's thinking of investing in the first
17:31
time for industrial IoT or
17:33
upgrading their systems, what
17:35
advice would you give them to start with? Let's start with
17:37
you, Chris. Well, I would say prepare
17:40
for the worst, but plan for the best. Think
17:43
about the different risks that are going to be associated
17:46
with this. From a business standpoint,
17:48
it's all about risk. Hackers use the term
17:51
exploitation, so do people with MBAs.
17:54
It's just a different way of thinking. So
17:56
start incorporating these types of things.
17:59
Hey, what would... the plan if this
18:01
happened. It doesn't have to be super long. It
18:03
can be incorporated directly into your current disaster
18:05
recovery plan. Speak with your suppliers.
18:08
If you don't feel comfortable enough
18:11
with speaking about
18:12
cybersecurity and privacy with your supplier,
18:14
you need to look for a new supplier.
18:16
Take a look at companies
18:19
and suppliers who participate
18:22
in different types of security conferences
18:25
or have their products looked
18:27
at by groups that do various
18:30
hacking villages. And if they're actively
18:32
looking at these things, that gives a good
18:34
deal of credence. And what about you,
18:36
Alison? What's the top level advice
18:39
you might give to a CEO investing in IoT
18:41
for the first time? I couldn't agree
18:44
more with Chris and those points. And obviously,
18:46
speaking from the other side of it, as a third
18:48
party supplier to the healthcare
18:50
industry, I think that partnership, that
18:52
understanding that if there's some
18:55
standardization of what is required,
18:57
and it's very clearly communicated
18:59
in that partnership, and we can comply quite
19:02
easily, open communication,
19:05
clear guidance and criteria of
19:07
what's needed is essential.
19:12
Big thank you to our guests, Chris Kubeska
19:14
from HyperSec and Alison Peace from Medtronic.
19:17
They're very useful insights into the industrial
19:19
IoT and keeping it secure. If
19:23
you're enjoying these kinds of insights, we have
19:25
many stories about the latest business tech
19:27
in secure futures. It's Kaspersky's
19:30
digital magazine about innovative top,
19:32
innovative leaders. And we've got articles
19:35
about new technologies in manufacturing
19:37
like digital twins, a video
19:39
and another interview with Chris again about the internet
19:42
of things and cyber threats in space, and
19:44
articles from last season's insight story,
19:46
including blockchain and digital truth.
19:49
You can find the link to secure futures in the
19:51
insight story show notes. The
19:56
fresh developments in the digital world are exciting,
19:59
but as new technology arrives, so
20:01
do new threats to our online safety. Providing
20:04
protection against those kind of threats is,
20:06
of course, what Kaspersky is all about. So
20:09
to give us some insight into the cybersecurity
20:11
challenges of the industrial Internet of Things and
20:13
how to keep it secure, I'm joined
20:16
by Dr. Armin Hazbini, Head
20:18
of Research Center, Middle East, Turkey and
20:20
Africa for Kaspersky's Global Research and
20:22
Analysis team, known as Great. They
20:25
spend all their time uncovering and understanding
20:27
the cyber threats that face us. So
20:29
Armin, give us an idea about the scale of
20:32
industrial IoT at the moment.
20:33
Well, according to a recent Kaspersky
20:36
study, more than 60% of
20:38
businesses maintain and run IoT
20:41
solutions for their own business and for their
20:43
clients. And a lot of these organizations
20:45
say that their IoT systems are not fully
20:47
protected. Close to half of the businesses
20:50
say that. And considering
20:52
that everyone's biggest concern is not
20:54
getting hacked, not having a breach or a leak
20:56
of data, not having the operations crippled
20:59
or destroyed. Well, security
21:01
requirements need to be in place for everyone.
21:04
Right. Though this is still not the case
21:06
and cybersecurity technologies are still
21:09
emerging on this front, specifically
21:11
for IoT devices and industrial
21:14
IoT devices. When we talk about
21:16
industrial IoT devices, we talk critical
21:18
infrastructure, water, power, energy
21:21
or others, and a shutdown or
21:24
a damage could cause a lot of harm. Sadly,
21:27
though, as per one of our surveys as
21:29
well, a third of these organizations
21:32
blame a lack of security or
21:34
a lack of budget for their inability to
21:36
deploy cybersecurity requirements for
21:38
all of their IoT systems. And
21:40
that is definitely a concern. Like
21:43
it makes us ask questions. If it
21:45
is not the resources or the employees, and
21:48
if it is not the budget, then what is
21:50
it? Is it the strategy? Is
21:52
it convincing top management? And questions
21:56
still do not have answers for many
21:58
organizations, sadly.
21:59
So what recommendations, if
22:02
we're talking not necessarily to a CSO,
22:04
an experienced person, but more to someone
22:06
on the board, what would you recommend that they
22:08
should be asking the questions of their IT
22:10
security team to really make sure these technologies
22:13
are safe?
22:13
Well, we should start with asking
22:15
technology vendors, because
22:17
technology vendors are still racing
22:19
for features and ignoring cybersecurity
22:22
requirements, like necessity requirements.
22:25
And then when a solution is demonstrated out of the
22:27
box, it's magnificent as a butterfly.
22:30
However, once implemented and confronting
22:32
real-life scenarios, it's vulnerable as
22:35
a butterfly as well, sadly. I
22:37
think on our side, we believe in technology that is
22:39
secure by design, secure in development
22:41
and in implementation. That
22:44
makes attacks worthless for
22:46
attackers, for criminals. On
22:48
our side, we have our Kaspersky OS and
22:51
the cyber immunity strategies. And
22:53
we've worked on a number of projects like railways,
22:56
interference protection or protecting power
22:58
grid vehicle charging devices. The
23:00
challenge starts on the top
23:03
level in each organization. It
23:05
becomes a priority on the top level, and
23:07
then it becomes translated into
23:09
policies, guidelines and practical methods
23:12
and methodologies used by technology
23:14
vendors and the operators inside
23:17
the organization, which is offering this IoT system
23:19
or solution.
23:22
Thank you very much to Amin. If
23:25
you're in the manufacturing, industrial or critical
23:27
infrastructure business, it really
23:29
is critical to make security a top
23:31
priority. Kaspersky ICS
23:33
CERT offers unique services in industrial
23:36
automation systems and Internet of Things
23:38
cybersecurity.
23:39
On the website, you can download the latest
23:41
free research reports and get advice about
23:43
protecting your industrial
23:44
enterprise. Check the link
23:46
in the show
23:47
notes. That's
23:51
it for this edition of In My Story, Tech Trends
23:53
and Past brought to you by Kaspersky. Search
23:56
for us wherever
23:56
you get your podcasts and click follow
23:58
so you don't miss an episode.
23:59
Coming up in this series we'll
24:01
be diving into the ethics of AI, exploring
24:04
how quantum computing is going to change everything
24:07
and talking about digital transformation.
24:10
How do you integrate technology into your business
24:12
and get a real understanding of it? If
24:15
you like using your hearing, please leave us a rating
24:17
and review. I'm sorry. It really
24:19
helps people find us and get the benefits of
24:22
all this great insight. If you
24:24
want to get ahead, you really can't afford
24:26
to miss it. Till next time. Goodbye.
24:29
Goodbye. Oh, hello. I'm
24:31
so sorry, Dot, about asking if you've been hacked.
24:34
That is OK.
24:34
I mean, it's like everything to say.
24:37
And you can ask the industry itself.
24:47
Just before I go, I wanted to tell
24:49
you about two other great series from Kaspersky
24:52
that you might like.
24:53
Fast Forward by Tomorrow Unlocked
24:55
explores the past, present and future of the
24:57
technologies around us. Season
24:59
two includes a very cool episode about
25:01
how digital twins can improve your personal
25:03
health. Plus, if you want to hear the latest
25:05
news and views from the world of cybersecurity,
25:08
join Jeff Esposito in the US
25:10
and David Buxton in the UK for Kaspersky
25:13
Transatlantic. They chat security
25:15
around current tech news and how
25:16
to low down all the latest native reaches.
25:18
You'll find links to both
25:20
these series in our show notes, but you'll also
25:23
find them wherever you get your podcasts. So
25:25
track them down and click follow so you don't
25:27
miss an episode.
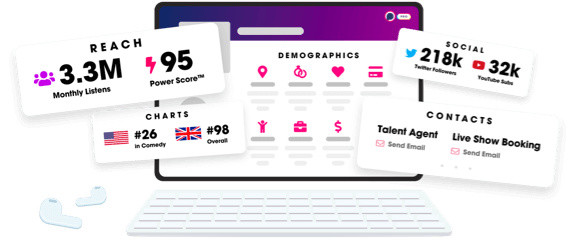
Unlock more with Podchaser Pro
- Audience Insights
- Contact Information
- Demographics
- Charts
- Sponsor History
- and More!
- Account
- Register
- Log In
- Find Friends
- Resources
- Help Center
- Blog
- API
Podchaser is the ultimate destination for podcast data, search, and discovery. Learn More
- © 2024 Podchaser, Inc.
- Privacy Policy
- Terms of Service
- Contact Us
